TCP and SSL selects layer four proxying: the ELB forwards targeted traffic with out modifying the headers. In a blended-use ecosystem wherever some ports are secured and others are left unencrypted, you can use the next annotations:In the over case in point, if the Services contained a few ports, 80 , 443 , and 8443 , then 443 and 8443 would use the SSL certification, but eighty would just be proxied HTTP. From Kubernetes v1. nine onwards you can use predefined AWS SSL policies with HTTPS or SSL listeners for your Solutions. To see which procedures are offered for use, you can use the aws command line instrument:You can then specify any 1 of these policies utilizing the ” assistance. beta. kubernetes. io/aws-load-balancer-ssl-negotiation-policy ” annotation for example:PROXY protocol aid on AWS. To enable PROXY protocol support for clusters running on AWS, you can use the pursuing provider annotation:Since model one. three. , the use of this annotation applies to all ports proxied by the ELB and are unable to be configured in any other case. ELB Accessibility Logs on AWS. There are many what-is-my-ip.co annotations to deal with accessibility logs for ELB Expert services on AWS. The annotation support. beta. kubernetes. io/aws-load-balancer-entry-log-enabled controls irrespective of whether entry logs are enabled. The annotation services. beta. kubernetes. io/aws-load-balancer-access-log-emit-interval controls the interval in minutes for publishing the entry logs. You can specify an interval of possibly five or 60 minutes. The annotation services. beta. kubernetes. io/aws-load-balancer-accessibility-log-s3-bucket-name controls the identify of the Amazon S3 bucket wherever load balancer access logs are saved. The annotation assistance. beta. kubernetes. io/aws-load-balancer-access-log-s3-bucket-prefix specifies the logical hierarchy you made for your Amazon S3 bucket. Connection Draining on AWS. Connection draining for Classic ELBs can be managed with the annotation company. beta. kubernetes. io/aws-load-balancer-relationship-draining-enabled set to the value of “true” .
The annotation services. beta. kubernetes. io/aws-load-balancer-relationship-draining-timeout can also be utilized to set greatest time, in seconds, to retain the current connections open up ahead of deregistering the scenarios. Other ELB annotations. There are other annotations to deal with Classic Elastic Load Balancers that are explained under. Network Load Balancer support on AWS. To use a Network Load Balancer on AWS, use the annotation services. beta. kubernetes. io/aws-load-balancer-sort with the value established to nlb . Unlike Common Elastic Load Balancers, Network Load Balancers (NLBs) forward the client’s IP deal with by to the node. If a Service’s . spec. externalTrafficPolicy is set to Cluster , the client’s IP deal with is not propagated to the end Pods. By environment . spec. externalTrafficPolicy to Community , the client IP addresses is propagated to the stop Pods, but this could result in uneven distribution of visitors. Nodes without having any Pods for a particular LoadBalancer Assistance will fall short the NLB Focus on Group’s wellbeing test on the vehicle-assigned . spec. healthCheckNodePort and not receive any traffic. In purchase to realize even targeted traffic, both use a DaemonSet or specify a pod anti-affinity to not track down on the exact node. You can also use NLB Companies with the inside load balancer annotation. In order for client visitors to attain cases at the rear of an NLB, the Node safety groups are modified with the subsequent IP guidelines:
- Can law enforcement officials trace Fb IP
- Exactly what do people young and old use your IP address
- Can citizens get IP address from Vimeo
- Might it be harmful if someone has found out your IP
- Is Ip resolved
- How do you disguise my Ip open
- Why Incognito is not really secure
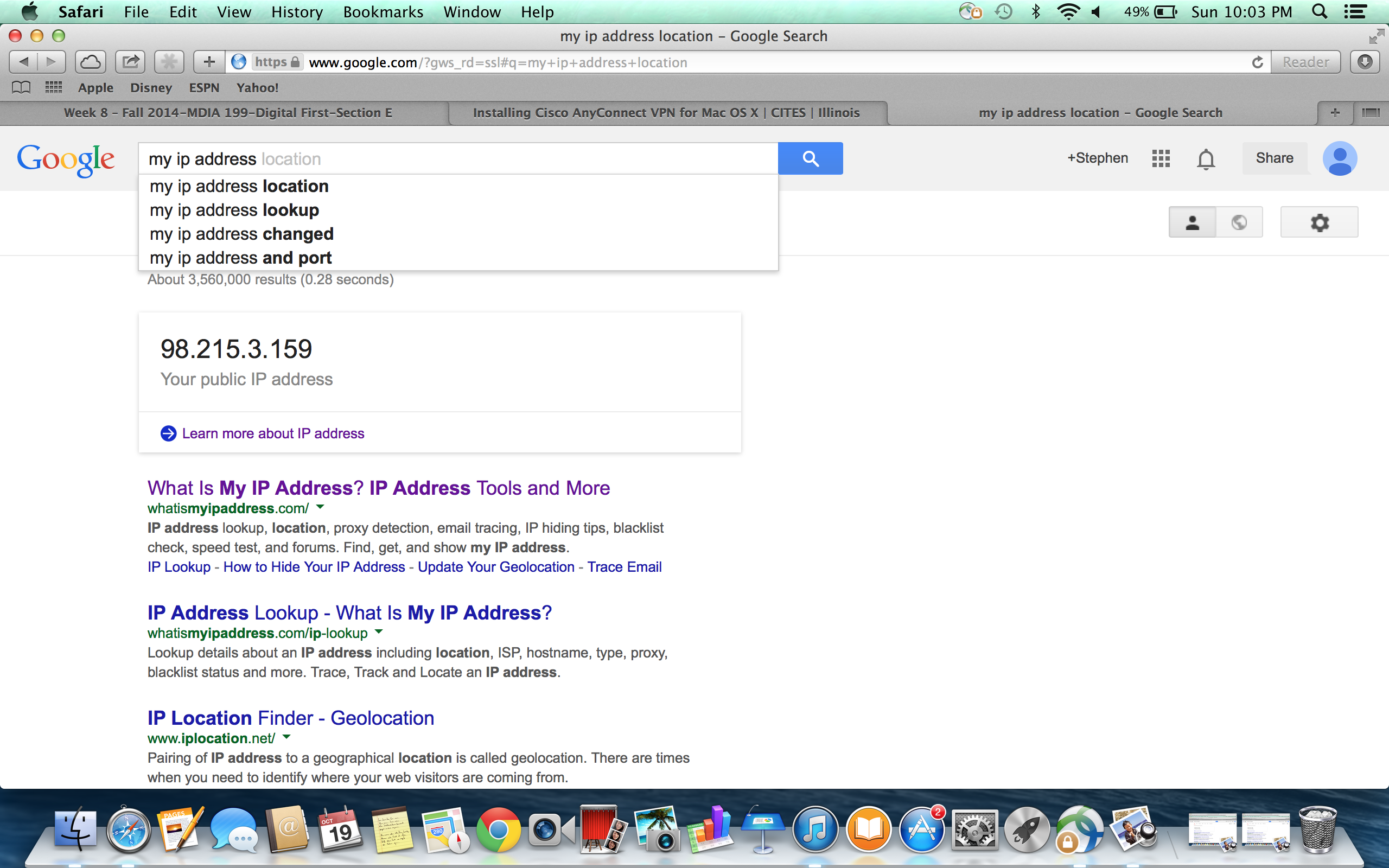
- How does one check out your IP
What are the 2 types of IP address
Rule Protocol Port(s) IpRange(s) IpRange Description Wellness Test TCP NodePort(s) ( .
